Data security
Data security refers to which users can see which data in the ThoughtSpot application.
Sharing and security privileges govern what data a user can access and what they can do with the data. Admins can use privileges to regulate access to information and provide a personalized user experience.
Users, groups, and privileges
Data security applies to users and groups. Users can be managed manually or through LDAP. Each user can have membership in one or more groups. Admins can make security settings that determine what users are allowed to do in ThoughtSpot. These settings are applied at the group level.
The following table shows the intersection of user privilege and ability:
|
|
Create/Edit WS
|
Create View
|
Create Embrace Connection
|
Modify Col. Props.1
|
Upload Data
|
Download Data
|
Share within Group
|
Share with all users
|
Manage RLS rules
|
CrUD Relationships
|
Read Relationships
|
See Hidden Cols
|
Join with Upload Data
|
Schema Viewer
|
Use Scheduler
|
Use Auto-Analyze
|
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Can administer ThoughtSpot | Y | Y | Y | Y | Y | Y | Y | Y | Y | Y2 | Y | Y | Y | Y | Y | Y |
|
Can upload user data
|
N | N | N | N | Y | N | Y | N | N |
Y3
|
Y4
|
N | N | N | N | N |
|
Can download data
|
N | N | N | N | N | Y | Y | N | N | N |
Y4
|
N | N | N | N | N |
|
Can manage data
|
Y | Y | Y | Y | Y | N | Y | N | N |
Y4
|
Y4
|
Y5
|
Y | N | N | N |
|
Can share with all users
|
N | N | N | N | N | N | Y | Y | N | N |
Y4
|
N | N | N | N | N |
|
Has SpotIQ privilege
|
N | N | N | N | N | N | N | N | N | N |
Y4
|
N | N | N | N | Y |
|
Can Administer and Bypass RLS
|
N | N | N | N | N | N | N | N | N | Y | N | N | N | N | N | N |
| None | N | N | N | N | N | N | Y | N | N | N |
Y4
|
N | N | N | N | N |
|
Table notes:
|
||||||||||||||||
Security model for sharing objects
You can share with groups and with individual users. Sharing of tables can be defined at the table, column, or row level. This provides flexibility in modeling your data security policy. Security and sharing settings apply to several different types of objects, each of which has its own security default settings and rules.
| Object type | Description | Default security model |
|---|---|---|
Tables |
The source data tables that have been loaded using ThoughtSpot Loader. |
Administrator users have access to source tables. They can share a table with other users or groups. See Sharing tables and columns. |
Columns |
The columns in the source data tables that have been loaded using ThoughtSpot Loader. |
Administrator users have access to columns in the source tables. They can share selected columns with other users or groups. See Sharing tables and columns. |
Rows |
The rows in the source data tables that have been loaded using ThoughtSpot Loader. |
All rows in the source tables are shared with all users by default. |
Imported data |
Data that was imported using a Web browser. |
Only the user who imported the data (and any user with administrator privileges) has access to it by default. They can share a table (or selected columns) with other users or groups. See Sharing tables and columns. |
Worksheets |
A worksheet created using a Web browser. |
Only the creator of the worksheet (and any user with administrator privileges) has access to it by default. They can share a worksheet with other users or groups. See Share Worksheets. |
Pinboards |
A pinboard of saved search results. |
Anyone who can view a pinboard can share it. See Share Pinboards. |
Understanding SHARABLE
When you share an object, only the users and groups that have SHARABLE set for the Sharing visibility option appear on the dialog.
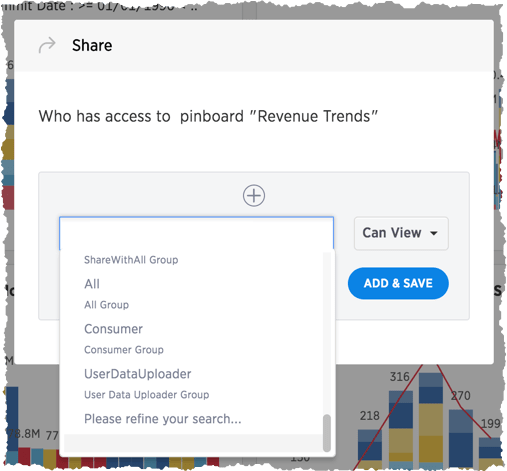
Only users in the Administrators group or users with Admin privileges can share with groups marked as NOT SHARABLE. Members of a group with Can share with all users authorization can also share with groups marked as NOT SHARABLE.
Users in groups marked NOT SHARABLE cannot share objects among themselves. In multi-tenant scenarios, admins can create groups that bring together portions of two non-share groups so that they can share. For example, the members of group C can share even if they belong to other groups that cannot.
Row level security
ThoughtSpot includes robust row level security, which allows you to filter all objects users see based on conditions you set at the level of row values in base data tables.
You may find it useful to create groups for RLS. To prevent these groups from appearing in the Share dialog, create a NOT SHARABLE group with a single user and an RLS group with another single user (1-to-1).
Related information



