Configure SSL
Secure socket layers (SSL) provide authentication and data security when sending data to and from ThoughtSpot.
You can use your own SSL certificate to secure ThoughtSpot HTTP(S) traffic.
ThoughtSpot Training
For best results with authentication and security, we recommend the following ThoughtSpot U course: Nginx SSL.
See other training resources at ThoughtSpot U.
About SSL
To enable SSL for the ThoughtSpot web service, you must provide your organization’s SSL certificate for the ThoughtSpot service URL. If you do not have this certificate, you have the following options:
-
Check with your IT department to see if they have an SSL certificate you can use.
-
Obtain the certificate from an issuing authority.
-
Use the default SSL certificate on the ThoughtSpot nodes.
-
Disable SSL from the Admin Console: Under SSL, select or .
ThoughtSpot supports a wide variety of SSL types.
Required ports
To use the ThoughtSpot web service securely, ensure that TCP port 443 is open to accommodate incoming connections to ThoughtSpot nodes and clusters.
Prerequisites
To add SSL and enable HTTPS in ThoughtSpot, you must generate the Certificate Signing Request (CSR) and obtain the SSL certificate chain and the private key.
Certificate Signing Request
When you generate a CSR, you handle sensitive data. Therefore, ThoughtSpot recommends that its customers generate their own CSRs.
You can generate a CSR in several ways. Most often, you generate a CSR and a new private key at the same time. If you already have a private key, use it to generate a CSR.
Follow these steps to generate a CSR and a private key. You need a computer you can run Linux commands on, and a recent version of openssl.
-
sshinto one of your ThoughtSpot nodes.ssh admin@<node_IP> -
Run the command to generate a CSR and private key pair:
openssl req -new -newkey rsa:2048 -nodes -out csr.pem -keyout pk.key[-subj "/key1=value1/key2=value with space/Note the following parameters:
-
ThoughtSpot supports a 2048 or 4096 bit key.
-
subj: a common subject. Logically equivalent to the-dnameproperty of keytool. Alternatively, you can skip this flag, andopensslprompts you to enter this information interactively. -
Optionally, run
add-multivalue-rdnto allow multiple values to be set for the same key. -
Run
man reqfor more details.
-
If you already have a private key, you can use it to generate a CSR. Follow these steps to generate a CSR with an existing private key:
-
sshinto one of your ThoughtSpot nodes.ssh admin@<node_IP> -
Run the command to generate a CSR and private key pair:
openssl req -new -key <private_key_file> -nodes -out csr.pem[-subj "/key1=value1/key2=value with space/Specify the existing private key file. Refer to the parameters listed above.
SSL certificate chain
The SSL certificate chain must be in PEM format, which is an X.509v3 file that contains ASCII (Base64) armored data, packed between BEGIN and END directives.
The certificate chain may contain a series of certificates, with the root certificate at the bottom and user-facing, while the ThoughtSpot-specific SSL certificate is at the top.
Private key
The private key must also be in compatible PEM format. It cannot be password-protected, or passphrase-protected.
| Do not use a passphrase when creating certificates with ThoughtSpot. |
If you are prompted to specify a passphrase, first check if it exists by invoking the following command:
openssl rsa -check -in pk.key`If the answer is 'yes', you must remove the passphrase first, and then proceed to use the private key with ThoughtSpot.
Configure SSL through the Admin Console
To configure SSL, navigate to the Admin Console by clicking on the Admin tab from the top navigation bar. Select SSL from the side navigation bar that appears.
Click Configure.
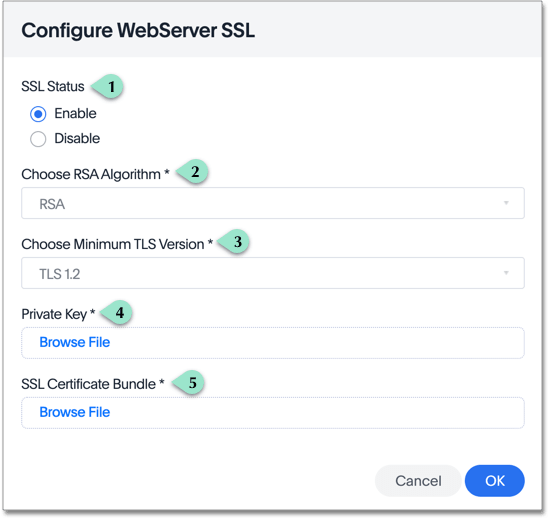
Fill out the following parameters:
-
Select Enable.
-
Choose RSA.
-
Choose TLS 1.2 as a best practice.
ThoughtSpot also supports TLS 1.1 and 1.0; set the minimum supported version to 1.1 or 1.0 to use these versions.
-
Attach your private key file.
-
Attach your SSL certificate bundle file.
Click OK.
Configuration string for load balancers
When enabling SSL support on a load balancer’s server-side SSL client profile, make sure to add support for the following ciphers to ensure compatibility between the load balancer and ThoughtSpot.
The following ciphers are currently supported:
| TLSv1.2:
| ciphers:
| TLS_DHE_RSA_WITH_AES_128_GCM_SHA256 - strong
| TLS_DHE_RSA_WITH_AES_256_CBC_SHA - strong
| TLS_DHE_RSA_WITH_AES_256_CBC_SHA256 - strong
| TLS_DHE_RSA_WITH_AES_256_GCM_SHA384 - strong
| TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256 - strong
| TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA - strong
| TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384 - strong
| TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384 - strong
| compressors:
| NULL
|_ least strength: strongThe cipher string would be as follows:
EECDH+AESGCM:EDH+AESGCM:AES256+EECDH:AES256+EDHYou can retrieve these from the ThoughtSpot web server (not against the load balancer) by running the following command on any ThoughtSpot node:
nmap --script ssl-enum-ciphers -p 443 <ThoughtSpot_node_IP_address>You must ensure that your load balancer supports these ciphers. If your load balancer cannot support these ciphers, contact ThoughtSpot Support.
Test the SSL certificate
To test if the certificate is installed correctly, see Sign in to the ThoughtSpot application.



